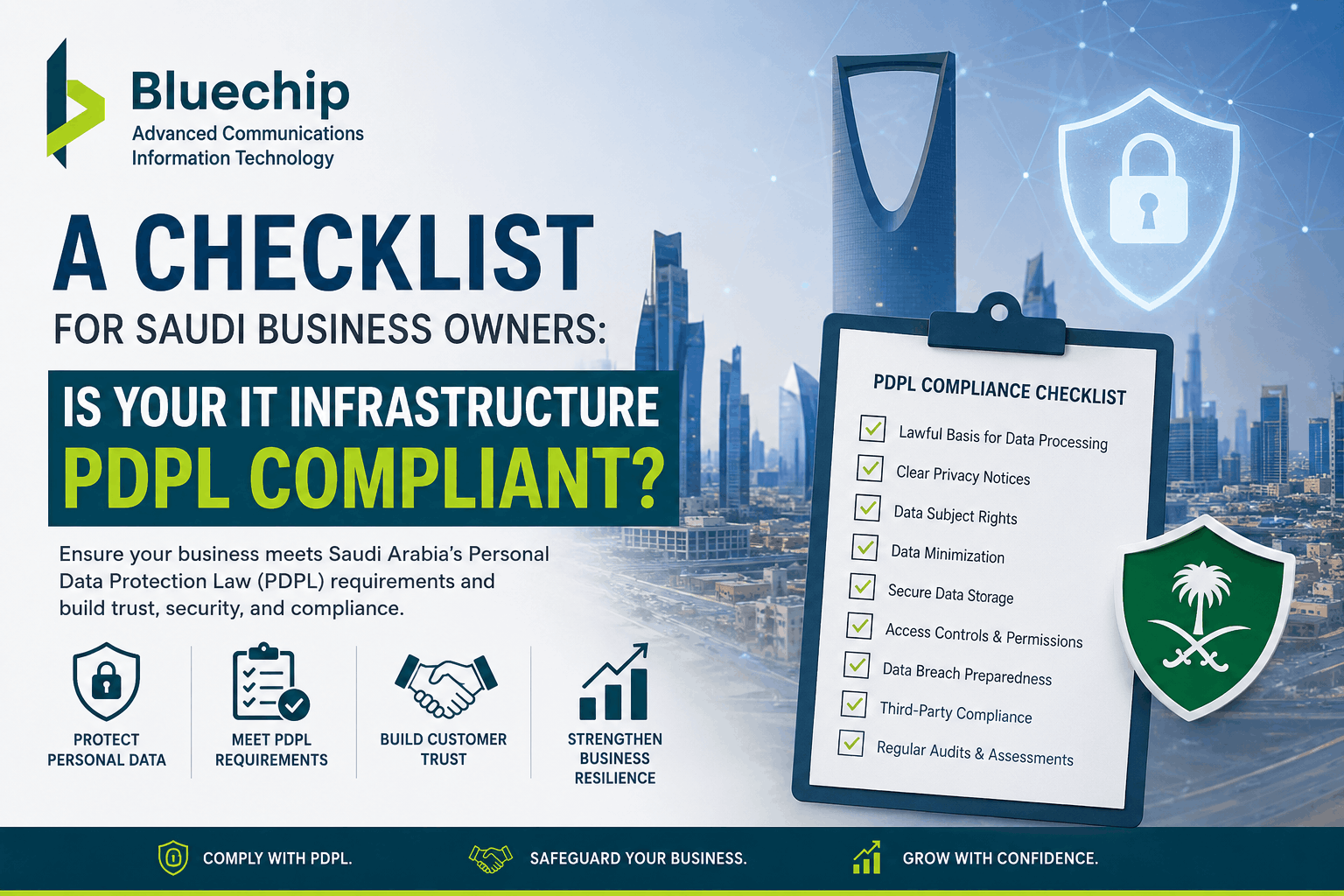
A Checklist for Saudi Business Owners: Is Your IT Infrastructure PDPL Compliant?
As Saudi Arabia continues accelerating its digital transformation under Vision 2030, businesses are collecting and processing more customer and operational data than ever before. With this rapid digital growth, data privacy and cybersecurity have become major priorities for organizations across the Kingdom.
This is where PDPL comes into focus.
The Personal Data Protection Law (PDPL) is Saudi Arabia’s primary data privacy regulation designed to protect personal information and strengthen cybersecurity practices for businesses operating in the Kingdom.
For many organizations, achieving compliance is no longer just a legal requirement — it has become an essential part of building customer trust and reducing cybersecurity risks.
Businesses increasingly work with professional cyber security companies in saudi arabia to evaluate infrastructure readiness and strengthen compliance frameworks effectively.
What is PDPL?
PDPL stands for:
Personal Data Protection Law
The law regulates how businesses collect, process, store, transfer, and protect personal data within Saudi Arabia.
PDPL applies to organizations handling personal information such as:
- Customer records
- Employee data
- Financial information
- Healthcare information
- Online user data
- Digital transactions
Businesses failing to meet compliance requirements may face penalties, reputational damage, and operational risks.
Why IT Infrastructure Matters for PDPL Compliance
PDPL compliance is not only about policies and documentation.
Businesses also need secure IT infrastructure capable of protecting sensitive information against:
- Unauthorized access
- Data breaches
- Ransomware attacks
- Insider threats
- Data loss incidents
Organizations investing in professional It Infrastructure Consulting Services in Saudi Arabia are better positioned to build secure, scalable, and compliant environments.
PDPL Compliance Checklist for Saudi Businesses
1. Identify and Classify Sensitive Data
Businesses should first understand:
- What data they collect
- Where data is stored
- Who has access
- How data is processed
Sensitive information should be categorized and monitored carefully.
Without visibility into business data, protecting it becomes extremely difficult.
2. Implement Strong Access Controls
Not every employee should have unrestricted access to sensitive information.
Businesses should implement:
- Role-based access control
- Multi-factor authentication (MFA)
- Strong password policies
- User activity monitoring
This helps reduce insider threats and unauthorized access risks.
3. Conduct Regular Security Risk Assessments
Cybersecurity threats evolve constantly.
Regular Security Risk Assessment activities help organizations identify vulnerabilities before attackers can exploit them.
A professional risk assessment typically evaluates:
- Network security
- Endpoint protection
- Server vulnerabilities
- Cloud security
- User access controls
- Backup systems
This helps businesses strengthen security posture proactively.
4. Secure Cloud and Remote Work Environments
Many Saudi businesses now rely on:
- Cloud applications
- Remote access
- Hybrid work models
- SaaS platforms
Without proper controls, these environments can expose sensitive data.
Businesses should secure:
- VPN access
- Cloud storage permissions
- Remote devices
- Mobile endpoints
- User authentication systems
5. Encrypt Sensitive Data
Encryption helps protect personal information even if systems become compromised.
Organizations should encrypt:
- Databases
- File storage
- Email communication
- Backup systems
- Cloud data transfers
This adds an important layer of protection for sensitive business information.
6. Maintain Backup and Disaster Recovery Plans
Data availability is a major part of compliance and business continuity.
Businesses should maintain:
- Automated backups
- Secure backup storage
- Disaster recovery procedures
- Recovery testing schedules
This helps minimize downtime during cyber incidents or system failures.
7. Monitor and Detect Cyber Threats
Continuous monitoring is essential for identifying suspicious activity quickly.
Businesses should deploy:
- Firewall protection
- SIEM monitoring
- Endpoint security
- Threat detection systems
- Network monitoring tools
Working with experienced cyber security companies in saudi arabia helps organizations improve threat visibility and incident response capabilities.
8. Train Employees on Data Protection
Human error remains one of the biggest causes of data breaches.
Employees should receive regular training on:
- Phishing awareness
- Password security
- Data handling policies
- Safe remote work practices
- Incident reporting procedures
Strong employee awareness significantly reduces cybersecurity risks.
9. Review Third-Party Vendor Security
Businesses often share sensitive information with external vendors and service providers.
Organizations should verify that vendors also follow proper data protection and cybersecurity practices.
Weak third-party security can create major compliance risks.
10. Maintain Compliance Documentation
PDPL compliance requires proper documentation and policy management.
Businesses should maintain records for:
- Security procedures
- Data processing activities
- Access logs
- Incident reports
- Employee training
- Risk assessments
Good documentation improves audit readiness and regulatory compliance.
Common Challenges Saudi Businesses Face
Many organizations struggle with:
- Legacy infrastructure
- Limited cybersecurity visibility
- Cloud security gaps
- Remote work risks
- Lack of internal expertise
- Compliance complexity
This is why businesses increasingly seek expert consulting and managed cybersecurity support.
Industries Most Affected by PDPL
PDPL compliance is especially important for:
- Healthcare organizations
- Financial institutions
- Government contractors
- E-commerce companies
- Educational institutions
- Logistics firms
- Telecom providers
These sectors handle large amounts of sensitive personal data.
Why Businesses Are Investing in Infrastructure Modernization
Modern IT infrastructure improves:
- Data protection
- Business continuity
- Compliance readiness
- Operational efficiency
- Cybersecurity resilience
Organizations modernizing infrastructure today are better prepared for future regulatory and cybersecurity challenges.
Trusted providers like Bluechip Advanced Technologies help Saudi businesses strengthen infrastructure security, compliance readiness, and long-term digital resilience.
Final Thoughts
PDPL compliance is becoming a critical business requirement across Saudi Arabia as digital transformation and cybersecurity risks continue growing.
Businesses that proactively strengthen IT infrastructure, improve cybersecurity monitoring, and conduct regular Security Risk Assessment activities will be better prepared to protect sensitive data and maintain regulatory compliance.
Organizations investing in secure infrastructure today are also building stronger trust with customers, partners, and stakeholders for the future.
Businesses seeking compliance-focused infrastructure and cybersecurity solutions can explore services offered by Bluechip Advanced Technologies for professional consulting and enterprise-grade security support.









