Acronis Cyber Protection is a comprehensive and easy-to-use solution that incorporates integrated backup, anti-malware, and recovery features into one safe and secure product to protect your data and devices. As an authorized Acronis Select Partner, Bluechip Tech is certified to provide Acronis’s advanced solutions to clients to guarantee the highest level of protection. Bluechip Tech’s technical team in Saudi Arabia is all trained through Acronis Academy and provides businesses the competency to be able to deploy, manage, and make the most of Acronis products in clients’ existing IT stacks.
This partnership also provides distributors and clients with several additional benefits, including exclusive resources, support, and competitive pricing. Therefore, organizations of all shapes and sizes have access to and options for utilizing reliable, trusted, and comprehensive cybersecurity solutions to keep their data safe.
Overview of Acronics Cyber Protection
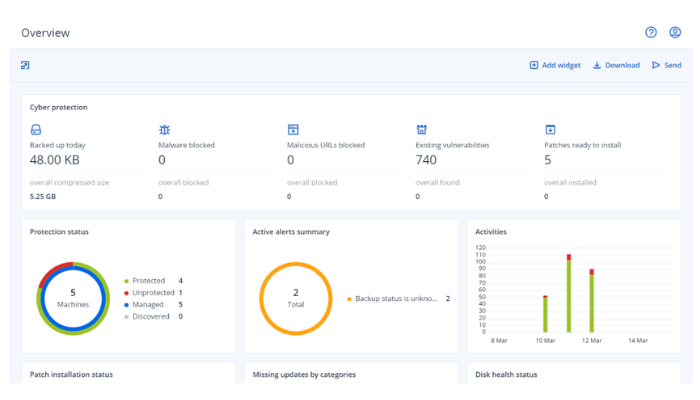
The Acronis Partner Program is recognized for its excellence. Acronis uses advanced technology like artificial intelligence and machine learning to identify and stop threats in real time, allowing for the potential to stop an infection before it infects your data. On the rare chance that a cyber-attack or data loss happens, Acronis allows you to recover your data and important files quickly and simply, so you can remain operational and productive without significant downtime. The company offers a comprehensive range of products, designed especially for business, to guarantee smooth IT operations.
Acronics Cyber Protection: Comprehensive Cyber Solutions Range
Here is what businesses can expect from the Acronics Cyber Protection offerings:

Continuous Data Protection
With continuous data protection, vital data can always be fully retained because every single change made in protected applications is backed up in real time. Any new data will always be protected, even if you must restore your system.
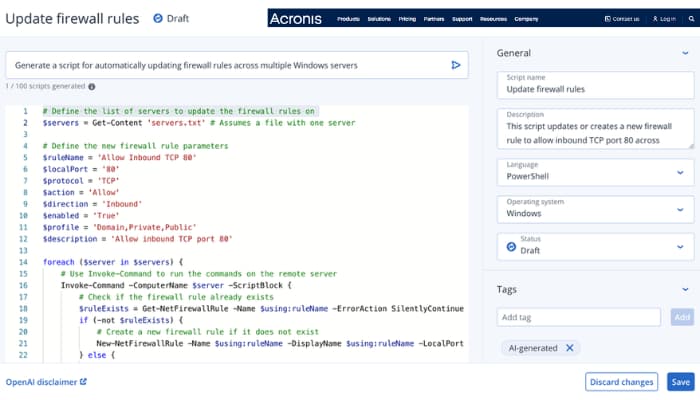
AI-Driven Cyber Scripting
Improve productivity and reduce human error by reducing comprehensive IT tasks with concentrated AI-driven scripting capabilities for effortless endpoint management.
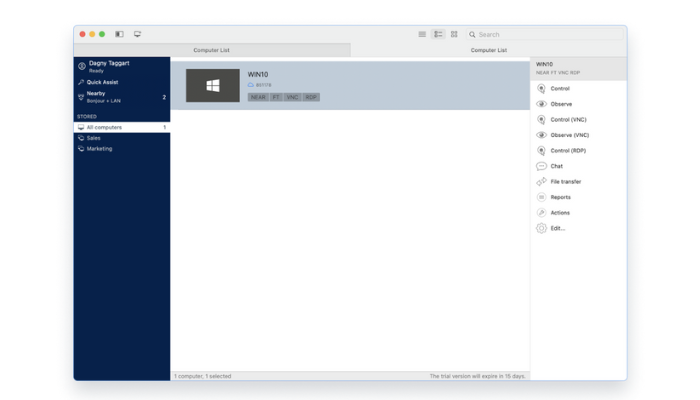
Remote Desktop Access
Businesses can access and manage Windows, macOS, and Linux systems securely over one platform that uses the proprietary NEAR protocol and is highly secure.
Global Threat Intelligence and Smart Alerts
Rather than waiting for a vendor-supplied threat intel feed, get instant notifications and real-time updates from the Acronis Cyber Protection Operation Centers (CPOC) regarding all events, including malware, vulnerabilities, and natural disasters.
Patch Management with Backup
When applying patches to software systems, do it with confidence. There is a fail-safe backup before each update, so if the patch causes issues, recovery can be completed very quickly.
Protect Against Ransomware
Change-based anti-malware scanning with automated malware removal during restoration makes it difficult to reinfect, and unchangeable storage maintains the integrity of backup file data.

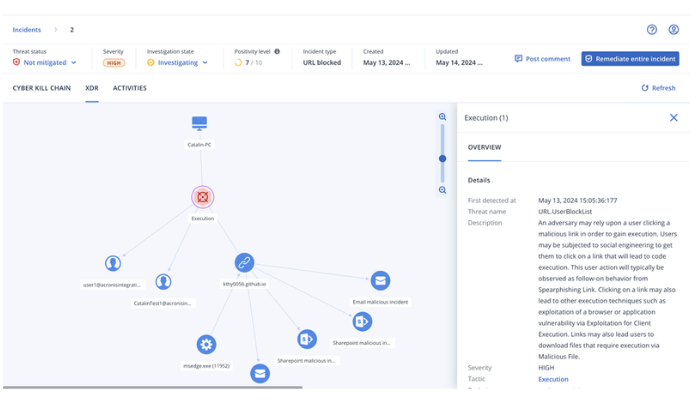
Advanced Threat Detection and Response (EDR)
Businesses in Saudi Arabia can identify and respond to any known or unknown cyber threats with advanced detection and analytical capabilities, and investigate and respond with confidence regarding what is taking place during an incident.

Forensic Backup Capabilities
Businesses can prepare for their compliance audits and potential digital investigations with disk-level backups that can capture everything they need to know, including memory dumps from running processes, using Forensic Mode.

Machine Learning-Based Monitoring
Machine learning monitoring improves your service response time, with predictive machine learning anomaly detection that will greatly reduce automated false alerts and allow technician's response time to be more efficient.

Cybersecurity with AI-Powered Defense
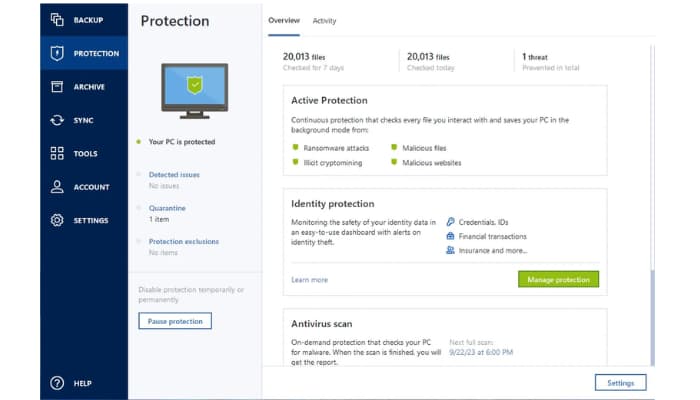
Protect Systems and data against advanced threats using behavioral damages and AI-based technology around antivirus, anti-malware, anti-ransomware, and anti-crypto jacking protections.

IT Asset Management
Keep full, up-to-date records of all hardware and software assets to help with lifecycle planning and upgrades.

Data Compliance and Protection Mapping
Businesses can automatically classify data. This allows regulatory compliance and prepares reports on where data is housed and its protection.

Key Features of Acronics Cyber Protection Solution
One must be aware of the essential specifications that Acronic’s cyber solutions offer:
- 100% Detection Rate Acronis Cyber Protection uses AI and machine learning to detect threats in real time with high accuracy. Its advanced mechanism facilitates any known and unknown cyber threat with just-in-time detection, which further gives businesses confidence in their cybersecurity infrastructure.
- 0% False Positives Acronis Cyber Protection tries to reduce false alerts with intelligent behavioral analysis and machine learning. This allows IT teams to address actual threats rather than false warnings, thus guaranteeing that operations flow well and threats are responded to correctly without fail.
- 100% High Availability: Acronis delivers the highest speed and reliability with reactive backup, remote access, and layers of AI-based automation. It aims to guarantee smooth IT operations, maximize limited downtime, and impart strong mitigation of threats in a sleek, high-performance framework of cybersecurity.
Bluechip Tech's Strategic Alliance with Acronis Cyber Protection
Acronis is revolutionizing data protection by putting ahead a simple, complete, and affordable set of cyber solutions for smaller and mid-sized companies. Their tools protect company information through backup, disaster recovery, and secure file sharing, all housed in one set of solutions. When it comes to Acronis, they protect against potential data loss from anything else: hardware failure, natural disasters, and more.
In the case of IT service providers like Bluechip Tech, Acronis offers a strong cloud-based it infrastructure that works under multiple users and levels of access. Through the cloud platform, it is extremely important to streamline everything from storage, operations, billing, and monitoring so that partners can sell services that are very fine-tuned and scalable for a large number of customers.













